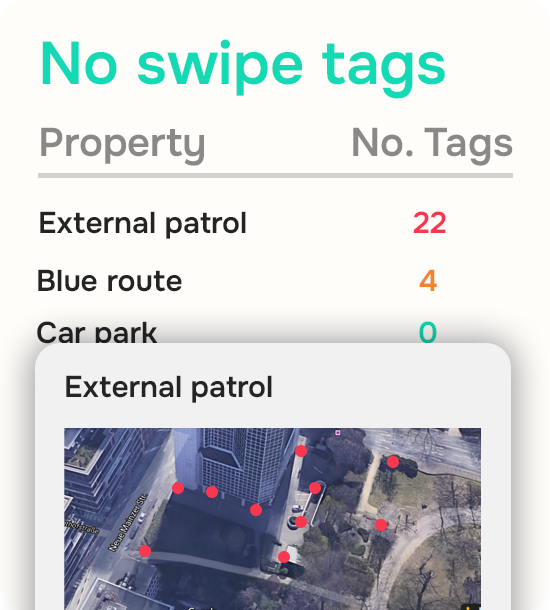
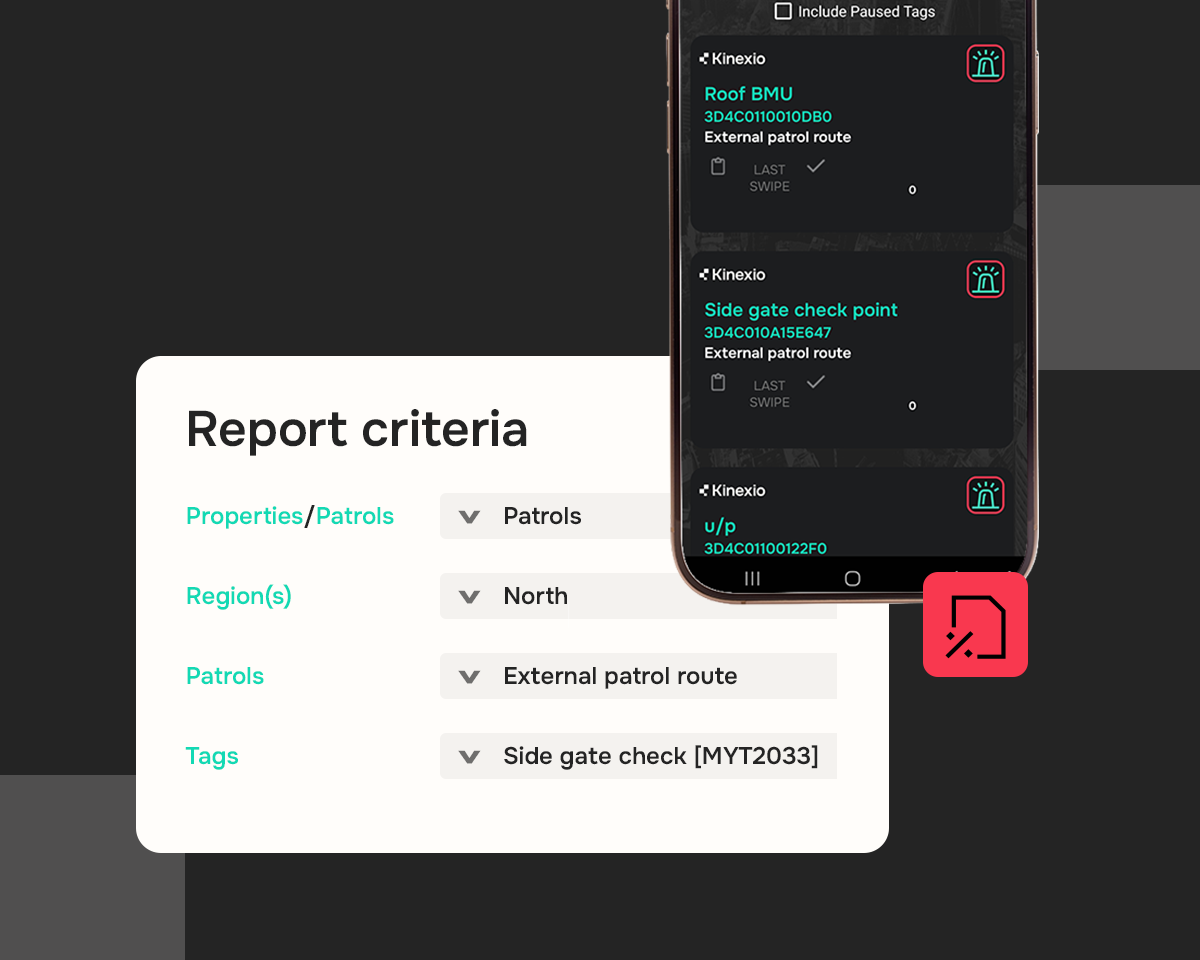
GPS-based systems improved visibility but only show proximity to a location, not interaction with specific checkpoints.
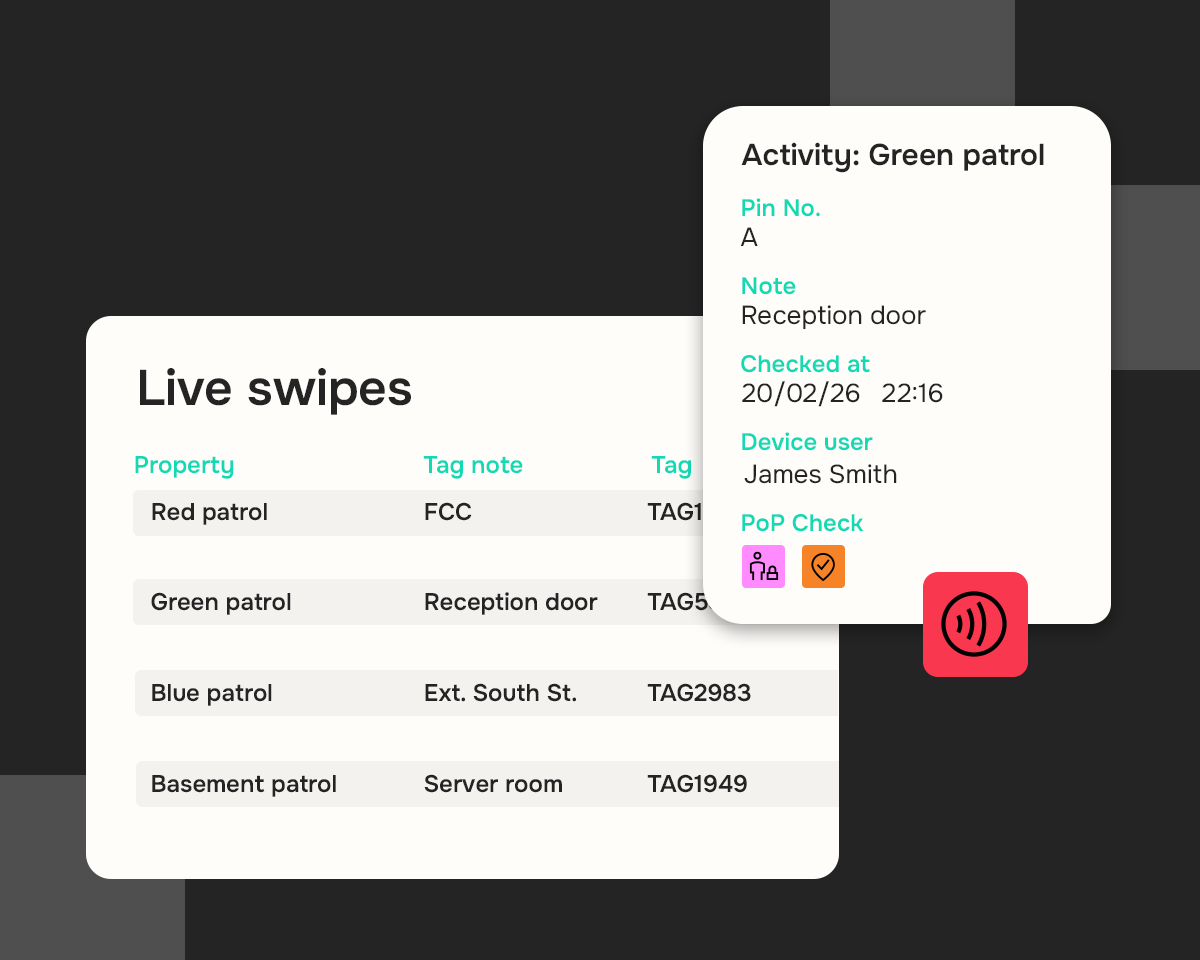
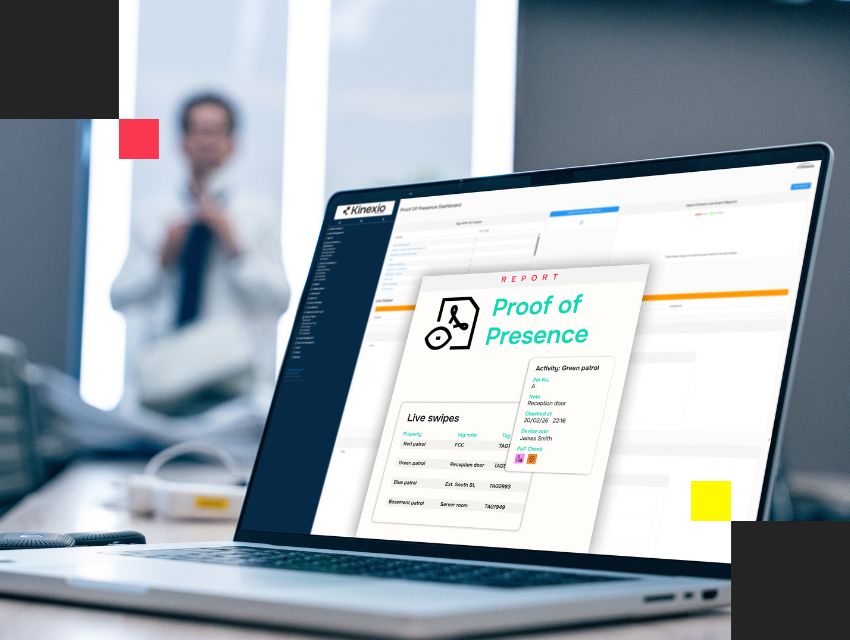
Without independent verification, operational certainty remained dependent on trust.
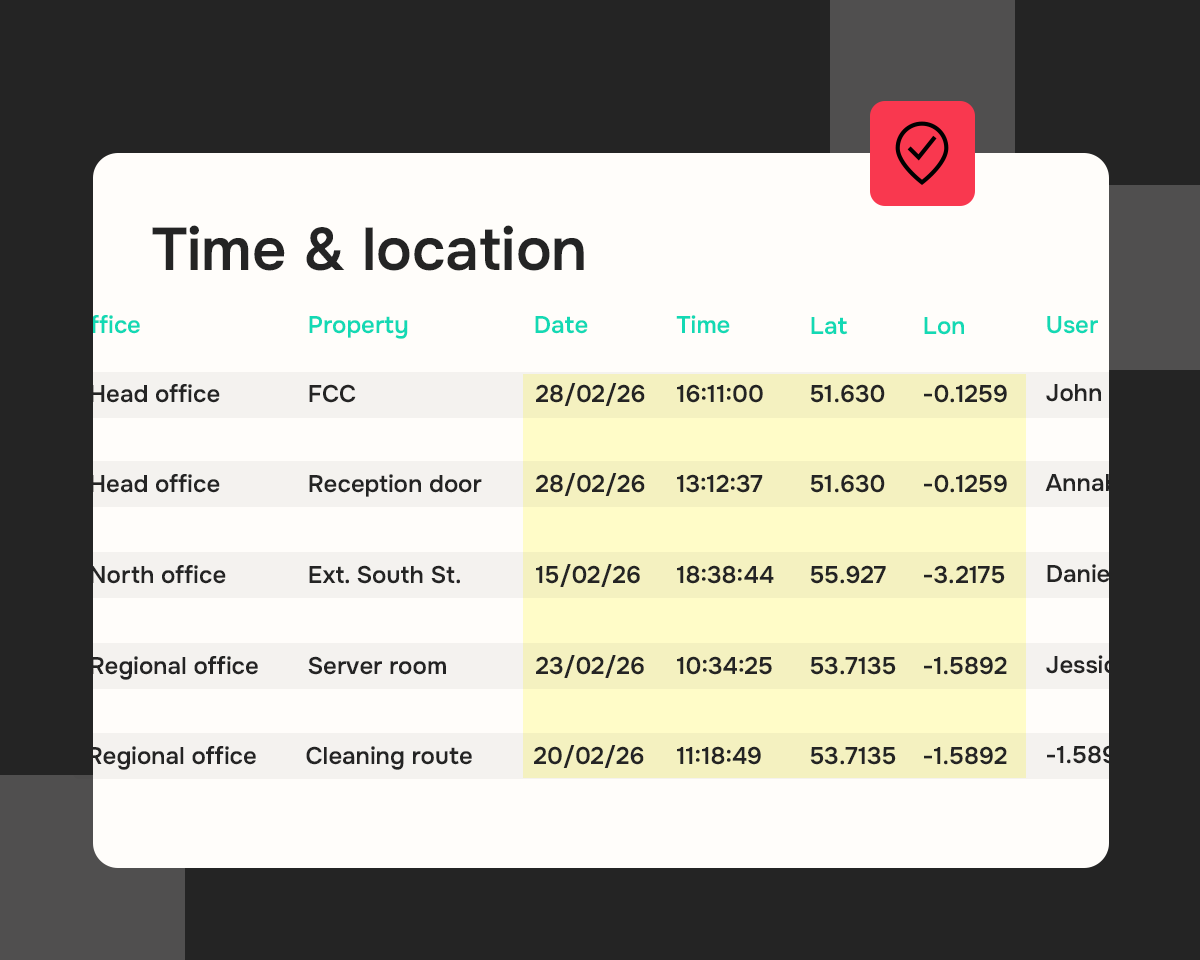
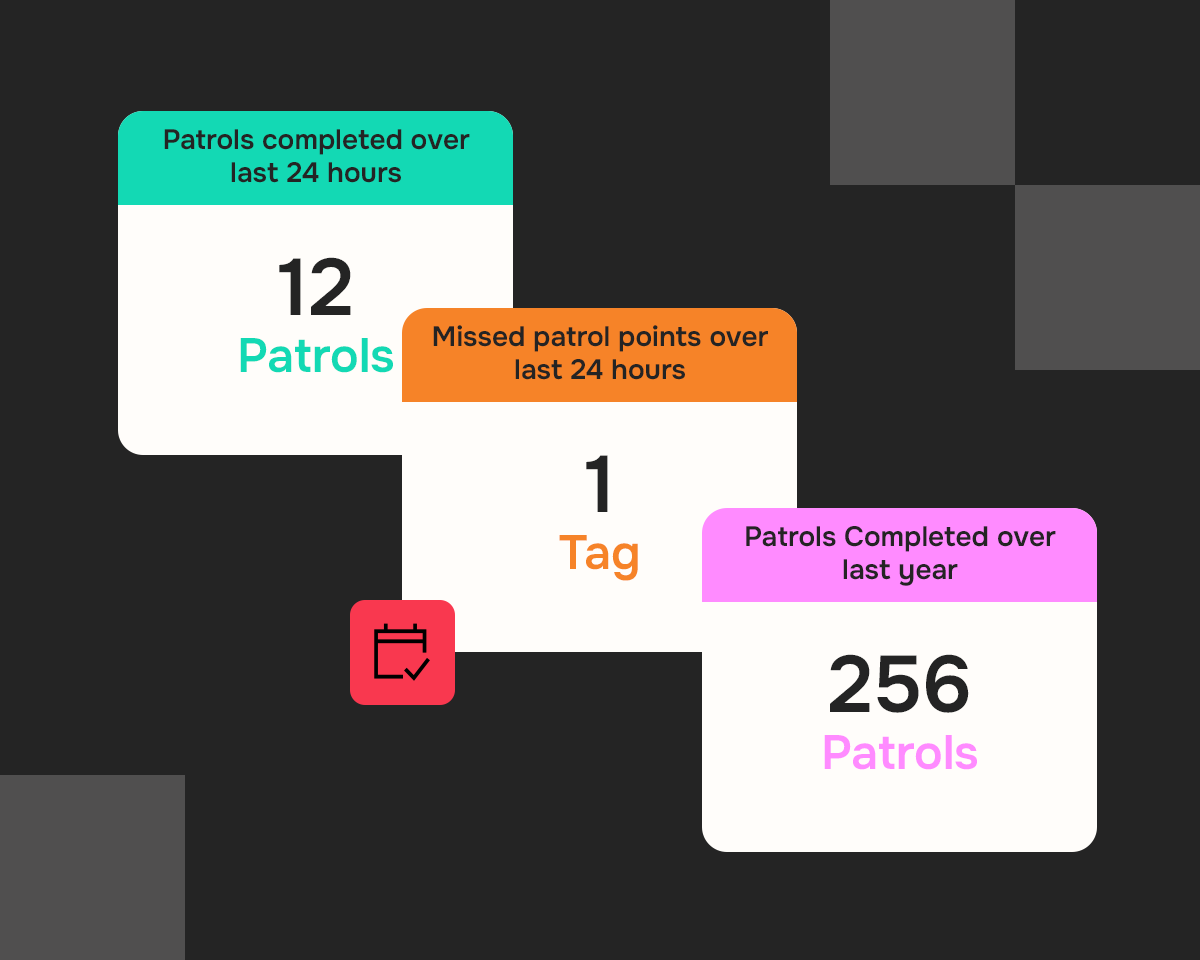
Proof of presence systems eliminate this uncertainty by independently verifying checkpoint interactions.