NFC system features
Security
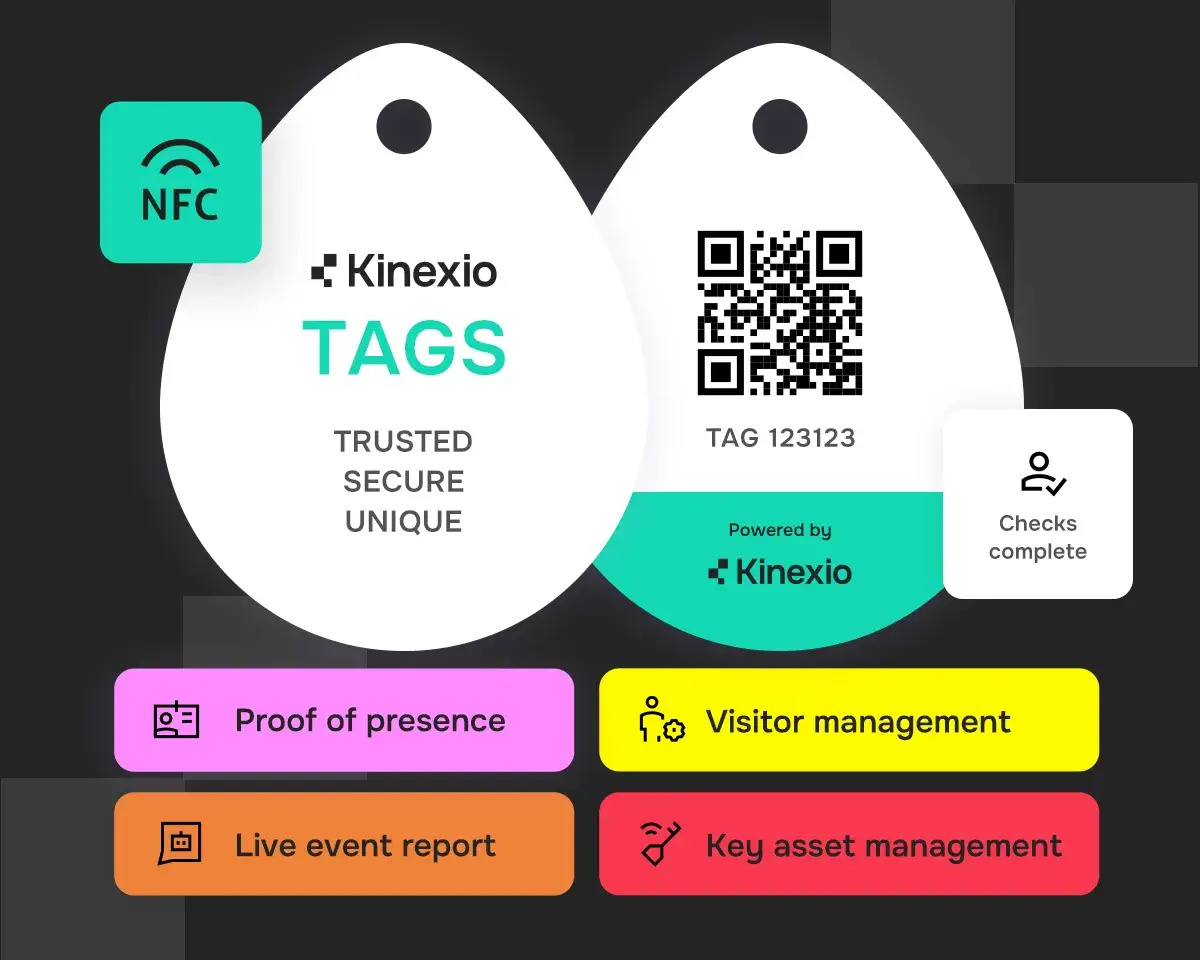
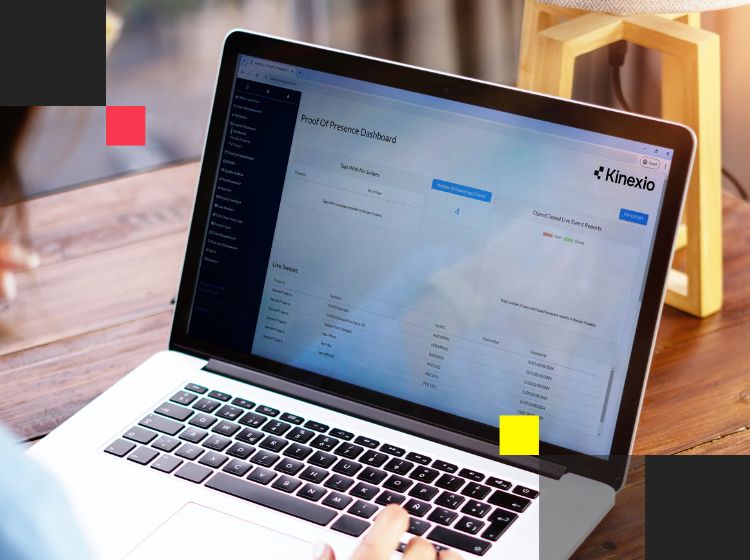
NFC Proof of Presence for patrols
Kinexio replaces paper patrol logs with secure NFC tags, delivering NFC Proof of Presence through real-time, tamper-proof scans. Each tap is logged with timestamp, user ID and exact location, ensuring accountability across every shift. Operatives use their smartphones or rugged scanners, even in low-signal areas using the Deadzone offline app. Whether you’re managing security patrols, cleaning rounds or building inspections, Kinexio ensures no checkpoint is missed and every action is recorded for audit.